ADT data breach exposes customer information
ADT confirms a new data breach exposing customer names, phone numbers and addresses. The cybercrime group ShinyHunters claims it stole millions of records.

ADT has confirmed a new data breach, and it comes with a familiar twist. A well-known cybercrime group is reportedly demanding money and threatening to leak data if it does not get paid.
The group behind it, ShinyHunters, says it stole more than 10 million records. ADT has not confirmed that number, but it says attackers accessed customer data.
According to the company, "ADT's cybersecurity systems detected unauthorized access to a limited set of customer and prospective customer data on April 20, and the company's response protocols activated immediately, terminating the intrusion, launching a forensic investigation with leading third-party cybersecurity experts, and notifying law enforcement."
Sign up for my FREE CyberGuy Report
GOOGLE CONFIRMS DATA STOLEN IN BREACH BY KNOWN HACKER GROUP
ADT says, "The investigation confirmed that the information involved was limited to names, phone numbers, and addresses. In a small percentage of cases, dates of birth and the last four digits of Social Security numbers or Tax IDs were included.
Here is the part that may bring some relief. ADT tells CyberGuy, "Critically, no payment information, including bank accounts or credit cards, was accessed, and customer security systems were not affected or compromised in any way."
Still, this kind of personal data carries real value. Even without full Social Security numbers, attackers can use it to build convincing scams that feel personal.
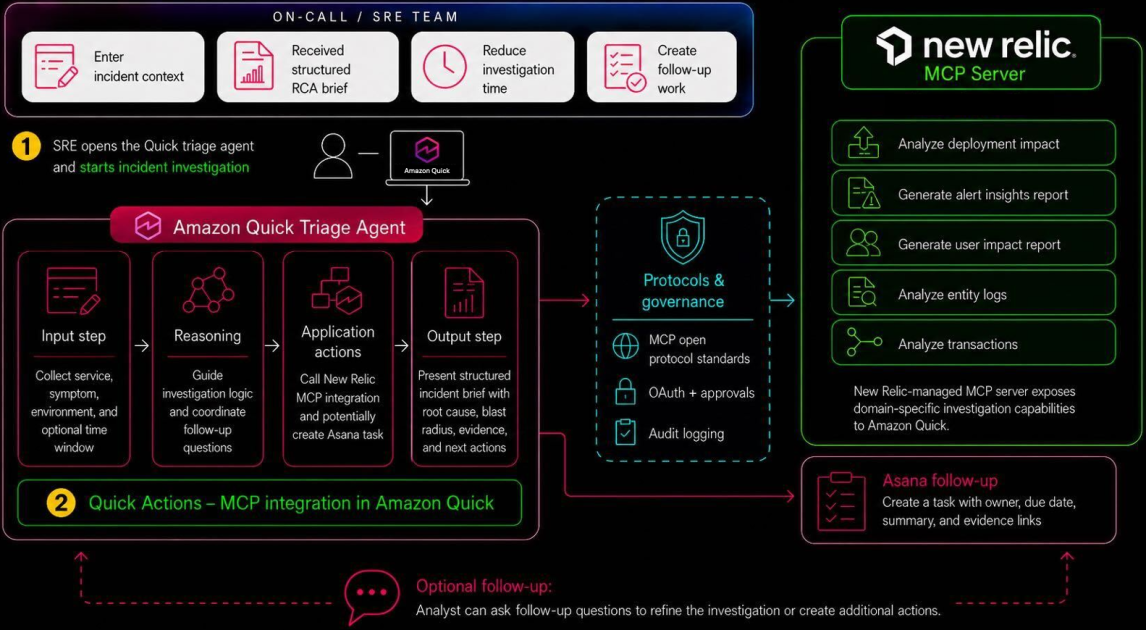
This breach may have started with a phone call. ShinyHunters told BleepingComputer it used a voice phishing attack, often called vishing, to compromise an employee's Okta single sign-on account. The group claims that access allowed it to steal data from ADT's Salesforce system. ADT has confirmed unauthorized access to customer and prospective customer data, but it has not publicly confirmed that specific attack method. This approach has become more common. Instead of hacking systems directly, attackers target people. One successful interaction can unlock multiple systems at once.
In a statement to CyberGuy, ADT said its response worked as intended.
"ADT's protocols performed as designed: the breach was identified quickly, the threat was contained, and the scope was limited," the company said. "ADT has directly notified all impacted individuals and will offer complimentary identity protection services as appropriate. Protecting customers is not just a priority; it is the foundation of what ADT does. The company remains committed to investing in and strengthening the cybersecurity infrastructure that its customers and their families depend on."
RANSOMWARE ATTACK EXPOSES SOCIAL SECURITY NUMBERS AT MAJOR GAS STATION CHAIN
On the surface, this breach may seem limited. No financial data. No system control. That sounds contained. The reality is more complicated.
Names, phone numbers and addresses create a powerful starting point for scams. Add even partial Social Security data, and the risk increases. Criminals can use that information to impersonate companies, reset accounts or trick victims into handing over more sensitive details.
This also raises a bigger issue. Even companies focused on security can become targets. That should change how you think about your own exposure.
This isn't the first time ADT has dealt with a data breach. The company disclosed incidents in August and October of 2024 that exposed customer and employee information.
When breaches happen more than once, it raises questions about internal security practices and how attackers keep finding a way in.
At the same time, it highlights a broader trend. Cybercriminal groups like ShinyHunters are focusing on identity systems and employee access instead of traditional hacking methods.
After a breach like this, the goal is to reduce how much attackers can do with your information and make yourself a harder target going forward.
If someone claims to be from a company like ADT, pause before responding. Scammers often use real details to sound convincing. Hang up and contact the company directly using a verified number.
Consider using a personal data removal service. These tools help remove your information from data broker sites, which reduces what scammers can find about you online. Check out my top picks for data removal services and get a free scan to find out if your personal information is already out on the web by visiting CyberGuy.com.
Identity theft monitoring can alert you to suspicious activity tied to your name or Social Security number early, which gives you a chance to act before damage spreads. See my tips and best picks on Best Identity Theft Protection at CyberGuy.com.
Use a password manager to create and store strong, unique passwords. If you reused passwords anywhere, especially on email or banking accounts, update them right away to prevent account takeovers. Check out the best expert-reviewed password managers of 2026 at CyberGuy.com.
HEALTHCARE DATA BREACH HITS SYSTEM STORING PATIENT RECORDS
Adding an extra login step, such as two-factor authentication (2FA), makes it much harder for attackers to break into your accounts, even if they have your credentials.
Make sure your devices run updated security software. Many modern tools can detect suspicious activity before it turns into a bigger problem.
If your Social Security number or even part of it may be involved, consider placing a credit freeze with the major bureaus. This prevents new accounts from being opened in your name without your approval.
Keep an eye on bank accounts, credit cards and important logins for unusual activity. Even small, unfamiliar charges or login alerts can be an early warning sign.
Install and maintain strong antivirus software on your devices. It can detect suspicious activity, block malware and help stop threats before they gain access to your data. Get my picks for the best 2026 antivirus protection winners for your Windows, Mac, Android and iOS devices at CyberGuy.com.
Attackers often try to reset your passwords using information they already have. If you get unexpected password reset emails or codes, treat them as a warning sign, not a routine message.
While ADT is one of the largest home security companies in the United States, the recent breach of customer information highlights potential vulnerabilities despite the company's assurance that home security systems were not compromised. There are many other options in the market, whether you prefer a professionally installed system or a do-it-yourself one.
For reference, you can check out my guide on the best home security systems at CyberGuy.com, where I’ve listed four of my favorite options. You might also want to find out if your home insurance offers a discount for installing robust security protection.
If your data was part of this breach, the risk does not end with the initial incident. In many cases, it is just getting started. You may begin to see more targeted scam calls or emails. Messages might include your name or reference your address to appear legitimate. That level of detail can make even cautious people hesitate. Even if you have never used ADT, this is a reminder of how often personal data circulates behind the scenes. Once it is out there, it can be reused in ways you never expected. The bigger takeaway is simple. Breaches like this are less about a single company and more about how exposed personal data has become across the board.
Should companies like ADT be doing a better job protecting your data, especially after repeated breaches? Let us know by writing to us at CyberGuy.com.
Sign up for my FREE CyberGuy Report
Copyright 2026 CyberGuy.com. All rights reserved.
























![KAIZEN Locations & Map Guide – Boss, Chest, Weapon, Style [KASHIMO]](https://www.destructoid.com/wp-content/uploads/2026/02/kaizen-locations-and-map-guide.jpg)




